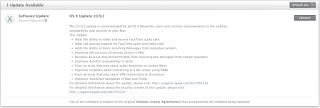
So, I turn on my old MacBook Pro this morning, and I get the following update notification:
Given #gotofail, can I actually trust this update?
Here is the list of things it supposedly fixes:
- Adds the ability to make and receive FaceTime audio calls
- Adds call waiting support for FaceTime audio and video calls
- Adds the ability to block incoming iMessages from individual senders
- Includes general improvements to the stability and compatibility of Mail
- Improves the accuracy of unread counts in Mail
- Resolves an issue that prevented Mail from receiving new messages from certain providers
- Improves AutoFill compatibility in Safari
- Fixes an issue that may cause audio distortion on certain Macs
- Improves reliability when connecting to a file server using SMB2
- Fixes an issue that may cause VPN connections to disconnect
- Improves VoiceOver navigation in Mail and Finder
- Improves VoiceOver reliability when navigating websites
- Improves compatibility with Gmail Archive mailboxes
- Includes improvements to Gmail labels
- Improves Safari browsing and Software Update installation when using an authenticated web proxy
- Fixes an issue that could cause the Mac App Store to offer updates for apps that are already up to date
- Improves the reliability of diskless NetBoot service in OS X Server
- Fixes braille driver support for specific HandyTech displays
- Resolves an issue when using Safe Boot with some systems
- Improves ExpressCard compatibility for some MacBook Pro 2010 models
- Resolves an issue which prevented printing to printers shared by Windows XP
- Resolves an issue with Keychain that could cause repeated prompts to unlock the Local Items keychain
- Fixes an issue that could prevent certain preference panes from opening in System Preferences
- Fixes an issue that may prevent migration from completing while in Setup Assistant
For detailed information about the security content of this update, see Apple security updates.
Going to http://support.apple.com/kb/HT1222 leads me to http://support.apple.com/kb/HT6150, which lists, among other things:
Data Security
Available for: OS X Mavericks 10.9 and 10.9.1
Impact: An attacker with a privileged network position may capture or modify data in sessions protected by SSL/TLS Description: Secure Transport failed to validate the authenticity of the connection. This issue was addressed by restoring missing validation steps.
CVE-ID
CVE-2014-1266
OK, so, it does look like Apple did issue an update about this vulnerability.
The question remains, can I trust this update?